Past Mistakes, Present Opportunities: Location-based Service Lessons for Consumer IoT
The pioneering vision of the Internet of Things (IoT), dating almost seventeen years into the past, is that of a ubiquitous society wherein people and "Things" are connected in an immersive networked computing environment, with the connected "Things" providing value to people or enterprises and their digital shadows, through intelligent social and commercial services.
In the recent past, two different perspectives of IoT have emerged depending on the level of automation: (i) Industrial and (ii) Consumer. Consumer IoT places humans as an integral part of IoT, and this underlying rationale differentiates itself from traditional automation or industrial IoT that has a strong machine-to- machine (M2M) flavor.
Humans not only benefit directly from consumer-centric IoT applications but are also active participants, serving directly or indirectly as sensors, actuators and control points. However, translating this idea to an achievable reality has been a work in progress for many decades with numerous hurdles to consumer adoption. In fact, the consumer IoT evolution bears a strong similarity to location-based services (LBS) which started as a commercial flop but then rediscovered itself to be the ubiquitous "on-the- go" technology that we all know. In this article, we aim to analyze the initial failure of LBS that consequently unfolded to set the stage for a major paradigm shift, and outline a workable roadmap for IoT business and technology based on the LBS footprint.
First generation LBS
The history of LBS dates back to the mid-nineties when the US government legislated in favor of E911 service, which allowed mobile network operators to locate emergency callers and share their information with Public Safety Answering Points. The service level agreement required operators to deliver location pointers at a prescribed accuracy level. To achieve this, many advanced positioning methods were developed to overcome the accuracy limitations posed by early cellular technology. Alongside this public service offering, operators introduced a series of commercial LBSs (such as the whereabouts of restaurants, gas stations, etc. in the user's vicinity) but this offering never succeeded in drawing significant user traction.
New generation LBS
It was not until ten years after the failure of the "first generation" model that interest in commercial LBS revived; but this time, with a new outlook. The emergence of GPS-enabled mobile devices, middleware technology (such as Web 2.0 that enabled context sharing) and mobile broadband transformed early LBS into a sophisticated service that was both exciting and helpful to consumers. This paradigm shift placed humans (and their social perimeter) at the center of the newly designed system (rather than operators or vendors) with feature-rich services that were proactive (rather than reactive), cross-referencing with multi-target position knowledge (as opposed to self-referencing, single target locations), and had a strong focus on applications (rather than content only) [2].
Key LBS lessons
The biggest factor behind the resurrection of LBS was the shift from operator-centric ownership and management of location data to user-centric modes of operation. FirstGen LBS solutions placed telecom operators as the primary entity for extraction of location data and content provisioning, without any involvement from the human subject. However, new generation LBS was driven more by humans with active control of the location content and distribution policies among peers.
LBS innovations in the form of novel middleware – coupled with cost reduction and availability of heterogeneous wireless interfaces – enabled a plethora of device-based localization techniques that could autonomously gather location data in multiple ways and leverage different positioning systems in a completely decentralized and ad hoc fashion. Location middleware could handle a large range of heterogeneous user contexts in a seamless, interoperable manner with any LBS provider using shared ontologies following semantic relationships. This allowed for simple reasoning on context descriptions that let the middleware identify content of interest by semantic matching of user interests and LBS properties despite their different representations. The wide adoption of XML-based descriptions (for representing user preferences, device characteristics, local resource availability, service properties and requirements, etc.) enabled open networking with LBSs. The access to context and its manipulation were facilitated through standard APIs that presented a generic interface for communicating with any LBS provider. The development of these features and ecosystems helped to reduce the time to market at competitive price points.
The change to user-centric design principles boosted confidence among users and alleviated their privacy concerns. In addition, techniques such as dynamic trust management and user-controlled privacy policies were introduced as part of the middleware to further reduce security and privacy fears. Due to the centralized operating model of traditional LBSs, credential checking operations such as authentication procedures were also centralized. As a result, the need for "always-available" internet connectivity became a rising bottleneck for "anytime, anywhere" LBS provisioning. NewGen LBS, in addition to this centralized approach, adopted distributed trust management techniques based on peer-to-peer dynamic trust chains (e.g., credential-based, reputation based, and social network-based) that blended in well with user-centric LBS scenarios. User-controlled privacy policies allowed preservation of location privacy by allowing users to configure local rules to expose their location data to services on a case-by-case basis and with varying levels of detail (e.g., city, street, building, or room number).
Closing remarks
Consumer IoT is in the same stage of infancy as the FirstGen LBS. While many of its potential benefits are real and achievable, the road to accomplish these may need a rethink as they are based on assumptions that favor an operator-centric view such as: cloud-centric data collection and analysis with centralized control, a closed ecosystem that is highly locked-in by vendors (where a single vendor owns the vertical application, platform, communication, services, and data), and connectivity that is always available [1,3].
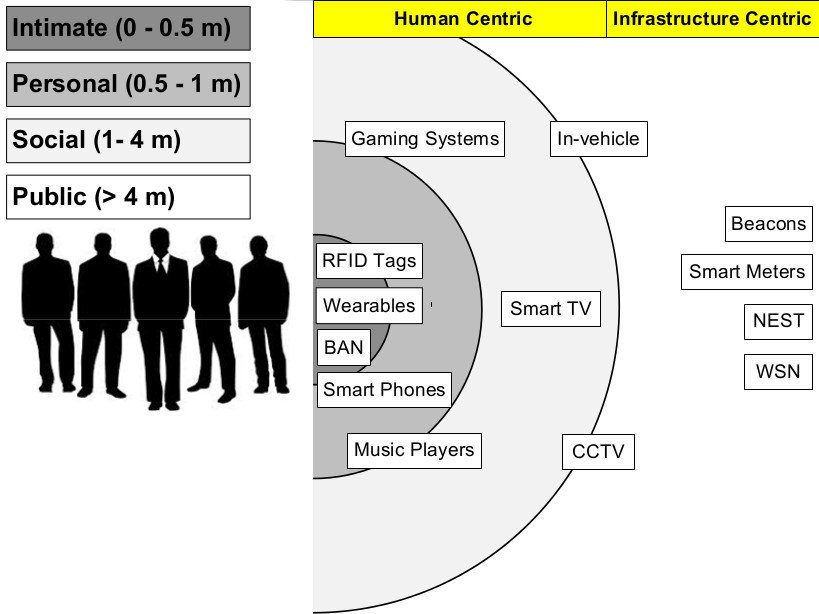
Inspired by the LBS evolution stages, the human-centric IoT model for consumer applications will reset the focus from what is enabled by the IoT infrastructure to the specific benefits that can be gained for humans who are part of, affected by and influence the network. As IoT is not just about a singular modality (as was the case with LBS), human-centric operations will bring about a tremendous focus on neighborhood and locality through the way people perceive, interpret and use their personal space. Here, the richness of information will be intense at close proximity to humans, but will diminish and become less interesting and useful as the proximity zone expands. In order to map out the closeness between humans and "Things", we use the proxemics theory of Edward Hall to classify devices (Figure 1) according to their spatial clues to humans (as intimate, personal, social and public). Here it is important to note that "Things" that are closer to humans often are more insightful, are ubiquitous and less tied to specific infrastructure. Bringing humans and their social elements (with their virtual online avatars such as social networks or media and virtual agents) will help span the digital and physical worlds, and also enable a better integration across humans and infrastructure. In essence, capturing proximity and interactions between humans and "Things", both in the physical and virtual worlds, would be necessary for actionable intelligence. This coupled with the design paradigm outlined in [1], [3] has the potential to overcome user apprehensions about the adoption of consumer IoT solutions.
Figure 1: Edward Hall's proxemic zones mapped to things
References
1. IP. Misra, Y. L. Simmhan, and J. Warrior, Towards a practical architecture for internet of things: An india-centric view.http://iot.ieee.org/newsletter/january-2015/towards-a-practical-architecture-for-internet-of-things-an-india-centric-view.html
2. P. Bellavista, A. Kupper, and S. Helal. Location-based services: Back to the future. IEEE Pervasive Computing, 7(2):85–89, April 2008
3. P. Misra, Y. L. Simmhan, and J. Warrior. Towards a practical architecture for the next generation internet of things. CoRR, abs/1502.00797, 2015
 Prasant Misra (S’08–M’12–SM’15) is a scientist at TCS Research and Innovation, TATA Consultancy Services, Bangalore. He received his Ph.D. from the University of New South Wales, Sydney in 2012. He performs research in low-power and energy-efficient sensing/signal processing/wireless communication with a focus on system design for CPS/IoT. He has many years of experience in scientific and industrial research. He has worked in different roles and capabilities for: Keane Inc. (a unit of NTT Data Corporation), CSIRO, SICS Swedish ICT and RBCCPS@IISc Bangalore; the outcomes of which have either resulted in commercial/open-source solutions or publications in premier sensornet/IoT forums. His professional contributions have been recognized by numerous awards, of which it is noteworthy to mention the ERCIM Alain Bensoussan, Marie Curie fellowship (2012) and the Australian Government's AusAID Australian Leadership Awards scholarship (2008). Currently, he is the secretary of IEEE Computer Society (Bangalore Section) and an Associate Technical Editor of IEEE Communication Magazine.
Prasant Misra (S’08–M’12–SM’15) is a scientist at TCS Research and Innovation, TATA Consultancy Services, Bangalore. He received his Ph.D. from the University of New South Wales, Sydney in 2012. He performs research in low-power and energy-efficient sensing/signal processing/wireless communication with a focus on system design for CPS/IoT. He has many years of experience in scientific and industrial research. He has worked in different roles and capabilities for: Keane Inc. (a unit of NTT Data Corporation), CSIRO, SICS Swedish ICT and RBCCPS@IISc Bangalore; the outcomes of which have either resulted in commercial/open-source solutions or publications in premier sensornet/IoT forums. His professional contributions have been recognized by numerous awards, of which it is noteworthy to mention the ERCIM Alain Bensoussan, Marie Curie fellowship (2012) and the Australian Government's AusAID Australian Leadership Awards scholarship (2008). Currently, he is the secretary of IEEE Computer Society (Bangalore Section) and an Associate Technical Editor of IEEE Communication Magazine.
Sign Up for IoT Technical Community Updates
Calendar of Events
IEEE 8th World Forum on Internet of Things (WF-IoT) 2022
26 October-11 November 2022
Call for Papers
IEEE Internet of Things Journal
Special issue on Towards Intelligence for Space-Air-Ground Integrated Internet of Things
Submission Deadline: 1 November 2022
Special issue on Smart Blockchain for IoT Trust, Security and Privacy
Submission Deadline: 15 November 2022
Past Issues
September 2022
July 2022
March 2022
January 2022
November 2021
September 2021
July 2021
May 2021
March 2021
January 2021
November 2020
July 2020
May 2020
March 2020
January 2020
November 2019
September 2019
July 2019
May 2019
March 2019
January 2019
November 2018
September 2018
July 2018
May 2018
March 2018
January 2018
November 2017
September 2017
July 2017
May 2017
March 2017
January 2017
November 2016
September 2016
July 2016
May 2016
March 2016
January 2016
November 2015
September 2015
July 2015
May 2015
March 2015
January 2015
November 2014
September 2014