Automating IoT Security: The EU CONCORDIA Approach
Industries and governments around the world continue to make great strides towards a vision of smart manufacturing, smart cities and the Internet of Things. The accelerating rate of this transformation has, unfortunately, outpaced our readiness to handle the security implications. Much of our critical infrastructure already depends on vast networks of low-cost embedded devices.
These devices are typically produced through a global supply chain that combines software and hardware from several different vendors into a single product.
Digital Sovereignty
Many vendors do not reveal their code or chip designs in order to protect their intellectual property. This raises some difficult questions: How can we trust devices if we have no right to see their design? Who is accountable if a design flaw leads to a costly security breach? Should vendors be compelled to update their products when these flaws are discovered? What if those vendors are no longer in business?
These concerns have led, in part, to a push for digital sovereignty in the European Union. CONCORDIA is an EU project established in pursuit of this goal. The project has recently grown to 55 partner institutions in both academia and industry across 19 countries and works closely with ENISA, EUROPOL, EDA and NATO’s CCDCOE [1]. CONCORDIA’s IoT strategy aims to automate and streamline credential management, remote attestation, firmware patching, certification, malware detection – essentially every aspect of device security – such that these operations become economical even for highly constrained devices.
Digital Identities for IoT Devices
Many IoT devices used in infrastructure projects are deployed in dangerous or difficult-to-reach places. Consider, for example, waste-water treatment plants, oil refineries, suspension bridges (e.g., structural health monitoring) and electrical substations. Performing frequent maintenance in these environments incurs a prohibitively high labor cost, so devices must remain operational for months or years without human intervention. Naturally, this precludes the use of any passwords or PIN codes. Devices must be configured to simply boot and establish a secure network connection automatically. In other words, each IoT device needs a unique digital identity to authenticate itself with.
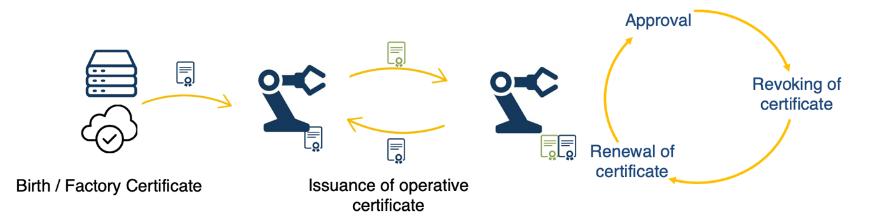
Figure 1: Digital identity provisioning and lifecycle for the IoT.
To address this challenge, our work has focused on developing automated, lightweight public key infrastructure (PKI) solutions for managing IoT credentials. Digital certificates and asymmetric cryptography have traditionally been viewed as “too heavy” for very small devices. Many network operators have, instead, opted for pre-shared keys (PSK) as a convenient alternative. However, PSK solutions do not provide authentication, key revocation or end-to-end security – these are only possible if each device has a unique identifier and secret key. Moreover, if an attacker compromises a network PSK, all devices need to be physically retrieved and provisioned with a new key.
In our recent work on the CEBOT project, we developed new lightweight protocols for certificate enrollment, re-enrollment, and compression that can run on virtually any device capable of running an IP network stack [2]. The enrollment protocol is now making its way through the IETF standardization process (see Figure 1) [3]. Our ongoing work in this area includes lightweight credential revocation and the integration of IoT PKI in the healthcare and automotive sectors.
Continuous Updates and Re-certification for IoT
The EU Cybersecurity Act of 2019 introduces for the first time an EU-wide security certification scheme for electronic devices [4]. This presents unique challenges for research and industry. In the case of safety certification, a rigorous process of testing and documentation endows a high level of confidence that a device will behave as expected. In contrast, history has shown time and again that every complex software system contains exploitable vulnerabilities. Hundreds are discovered in the Linux kernel every year [5].
In practice, security depends on our ability to issue software updates patches as soon as vulnerabilities are discovered. There are three basic building blocks required to automate this process on IoT devices, namely:
- Digital certificates backed by a reliable PKI are needed in order to sign firmware images. For encrypted updates, digital certificates also provide the basis for end-to-end security between devices and update authors.
- A trusted execution environment (TEE) on each device provides hardware-enforced isolation of security-critical software.
- A small amount of trusted immutable code (i.e., the trusted computing base, or TCB) with exclusive access to the device hardware root of trust.
The TCB code executes in a TEE and is responsible for installing firmware updates on the device, and for providing the device owner with a cryptographic proof that this has been done correctly – a process known as remote attestation. The advantage of this approach is that only the TCB and the hardware itself is fully trusted. The operating system and application code are complex and therefore likely to require security patches.
Ultimately, our objective is to create an automated re-certification solution, whereby devices can be issued with an EU-backed security certification that is valid until a vulnerability is discovered. When this occurs, devices must be patched and re-certified without any physical interaction. There are already ongoing efforts in the IETF SUIT working group to standardize the distribution of firmware updates and metadata [6]. Our primary research focus in this area is the implementation of TEEs on open-source RISC-V architectures. Currently, TEEs in the embedded and cloud spaces are dominated by ARM TrustZone and Intel SGX, respectively. Developing future IoT devices on open-source platforms has the potential to bolster consumer confidence that the security claims about a device are correct, and to accelerate the discovery and patching of vulnerabilities.
Threat Intelligence at the Network Edge
For the foreseeable future, most IoT devices will contain closed-source IP manufactured, at least partially, in another country. This raises concerns for many about attacks on the supply chain, hidden backdoors or pre-installed malware for data exfiltration. Most importantly, compromised devices must not become a source of attacks against the wider Internet (see Mirai DDoS attack). One mitigation strategy we are investigating is threat intelligence at the network edge. This entails analyzing network traffic in real-time with federated machine learning on the network border router in order to detect malicious behavior on the part of devices within the network. This approach is in line with privacy by design and default as envisioned by GDPR (as opposed to exporting and processing all data on the cloud).
Conclusion
The European Union has introduced an IoT security certification framework for ICT products and services. No device should be declared secure unless it can be securely and dependably updated in the future. Given the scale and sprawl of the IoT, it is crucial that devices can be managed, updated and re-certified remotely. Additionally, networks must be protected against IoT devices, which we aim to accomplish through federated machine learning at the network edge. The EU CONCORDIA project connects academic and industrial institutions in order to develop scalable and automated solutions to these challenges.
References
- https://www.concordia-h2020.eu
- J. Höglund, S. Lindemer, M. Furuhed, and S. Raza, “PKI4IoT: Towards Public Key Infrastructure for the Internet of Things,” Computers & Security, p. 101658, Nov. 2019.
- https://datatracker.ietf.org/doc/draft-ietf-ace-coap-est/
- https://ec.europa.eu/digital-single-market/en/eu-cybersecurity-act
- https://www.cvedetails.com/product/47/Linux-Linux-Kernel.html?vendor_id=33
- https://datatracker.ietf.org/group/suit/about/
 Samuel Lindemer received his B.Sc. in Electrical Engineering from Northeastern University in Boston, MA in 2017. In 2019, he completed his M.Sc. in Embedded Systems at KTH Royal Institute of Technology in Stockholm, Sweden and began his industrial Ph.D. studies at RISE Cybersecurity and Uppsala University. His current research focus is on trusted execution environments on embedded RISC-V architectures.
Samuel Lindemer received his B.Sc. in Electrical Engineering from Northeastern University in Boston, MA in 2017. In 2019, he completed his M.Sc. in Embedded Systems at KTH Royal Institute of Technology in Stockholm, Sweden and began his industrial Ph.D. studies at RISE Cybersecurity and Uppsala University. His current research focus is on trusted execution environments on embedded RISC-V architectures.
 Anum Khurshid is a Ph.D. student at RISE Cybersecurity and Uppsala University in Sweden. She completed her M.Sc. in Computer Science with a specialization in Cybersecurity in 2017 from COMSATS University in Pakistan. Her current research is focused on security for resource-constrained IoT, including software security and trusted execution environments in the ARM TrustZone ecosystem.
Anum Khurshid is a Ph.D. student at RISE Cybersecurity and Uppsala University in Sweden. She completed her M.Sc. in Computer Science with a specialization in Cybersecurity in 2017 from COMSATS University in Pakistan. Her current research is focused on security for resource-constrained IoT, including software security and trusted execution environments in the ARM TrustZone ecosystem.
 Han Wang received a double M.Sc. in Computer Science from Uppsala University and National Taiwan Normal University in 2017. She is currently an industrial Ph.D. student at RISE Cybersecurity and Uppsala University. Her current research focus is on machine learning for IoT security.
Han Wang received a double M.Sc. in Computer Science from Uppsala University and National Taiwan Normal University in 2017. She is currently an industrial Ph.D. student at RISE Cybersecurity and Uppsala University. Her current research focus is on machine learning for IoT security.
 Martin Furuhed works as a product manager at Nexus Group in Sweden, responsible for the Certificate Manager CA platforms and has experience from the PKI industry since 1998. He is active in, and is driving, several projects extending and adapting traditional PKI solutions for IoT scenarios for both industries and the public sector.
Martin Furuhed works as a product manager at Nexus Group in Sweden, responsible for the Certificate Manager CA platforms and has experience from the PKI industry since 1998. He is active in, and is driving, several projects extending and adapting traditional PKI solutions for IoT scenarios for both industries and the public sector.
 Shahid Raza received his M.Sc. degree from KTH Royal Institute of Technology in Stockholm, Sweden, and his Industrial Ph.D. from RISE SICS in Stockholm and Mälardalen University in Västerås, Sweden in 2013. He is an expert researcher and the Director of RISE Cybersecurity, where he has been involved with research since 2008. Shahid is also an Associate Professor at Uppsala University Sweden. His current research interests include all aspects of IoT security.
Shahid Raza received his M.Sc. degree from KTH Royal Institute of Technology in Stockholm, Sweden, and his Industrial Ph.D. from RISE SICS in Stockholm and Mälardalen University in Västerås, Sweden in 2013. He is an expert researcher and the Director of RISE Cybersecurity, where he has been involved with research since 2008. Shahid is also an Associate Professor at Uppsala University Sweden. His current research interests include all aspects of IoT security.
Sign Up for IoT Technical Community Updates
Calendar of Events
IEEE 8th World Forum on Internet of Things (WF-IoT) 2022
26 October-11 November 2022
Call for Papers
IEEE Internet of Things Journal
Special issue on Towards Intelligence for Space-Air-Ground Integrated Internet of Things
Submission Deadline: 1 November 2022
Special issue on Smart Blockchain for IoT Trust, Security and Privacy
Submission Deadline: 15 November 2022
Past Issues
September 2022
July 2022
March 2022
January 2022
November 2021
September 2021
July 2021
May 2021
March 2021
January 2021
November 2020
July 2020
May 2020
March 2020
January 2020
November 2019
September 2019
July 2019
May 2019
March 2019
January 2019
November 2018
September 2018
July 2018
May 2018
March 2018
January 2018
November 2017
September 2017
July 2017
May 2017
March 2017
January 2017
November 2016
September 2016
July 2016
May 2016
March 2016
January 2016
November 2015
September 2015
July 2015
May 2015
March 2015
January 2015
November 2014
September 2014


